NullCon CTF: Reverse Level 5 (500 points)
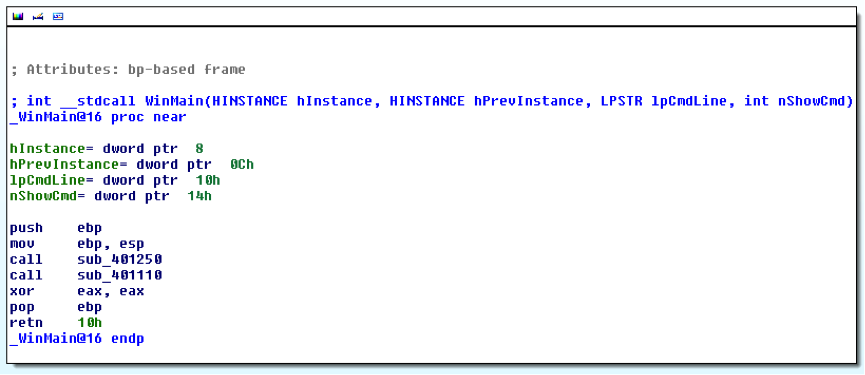
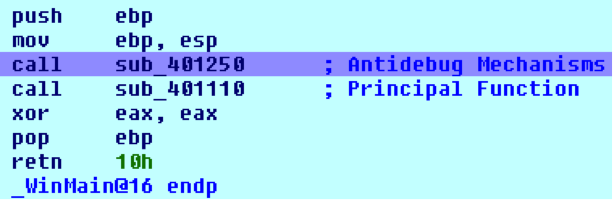
The first thing I did was making a static analysis. When you open the executable with IDA Pro, the first thing you see is the WinMain function:
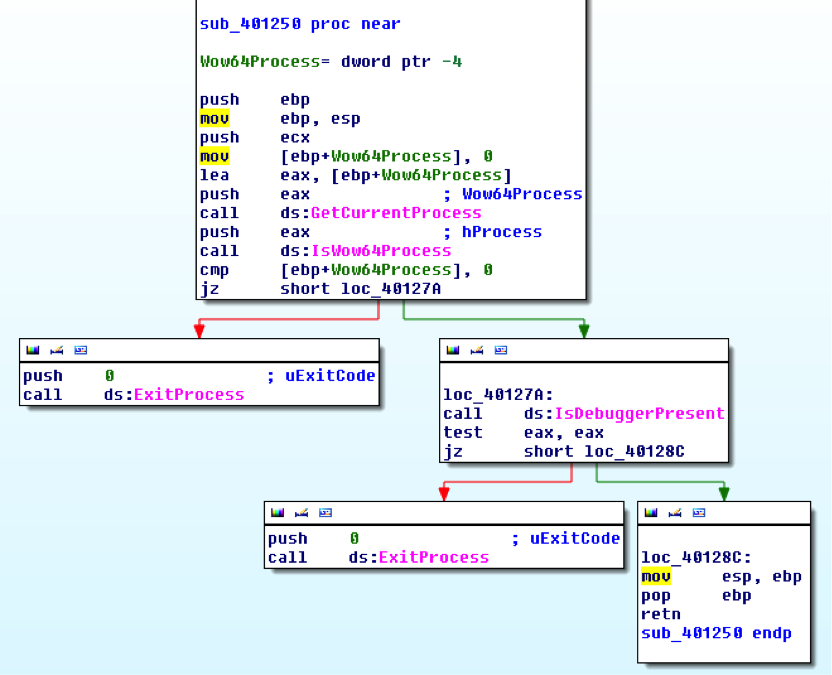
Analyzing the first function of WinMain (Sub_401250), you can see that it contains anti-debug mechanisms, so when the program is run, it will have put a break point and change EIP value for skip this function:
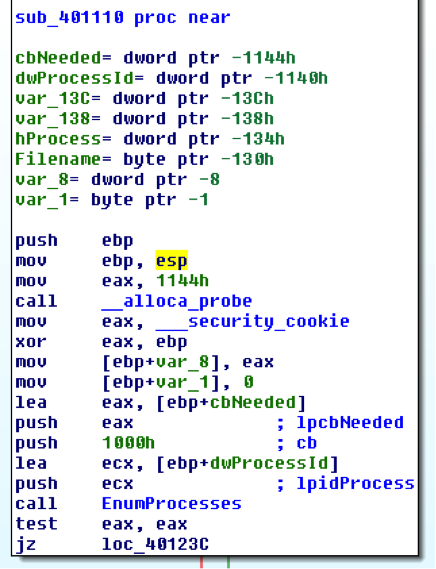
Once I saw what the first function did, I went to the second function of WinMain (sub_401110), the first thing this function does is listing the processes for one:
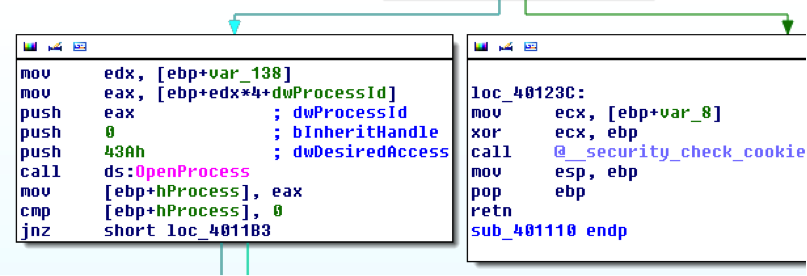
When it identifies a process, opens and gets the name by calling «OpenProcess»:
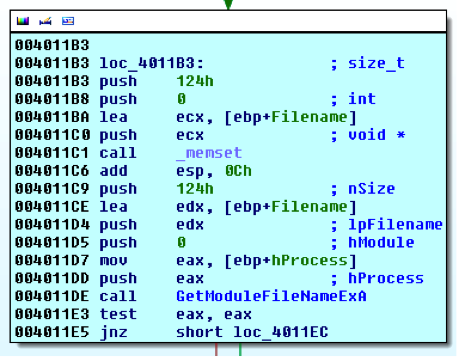
Once opened the process, it compares the name to see if it corresponds to the «explorer.exe» process:
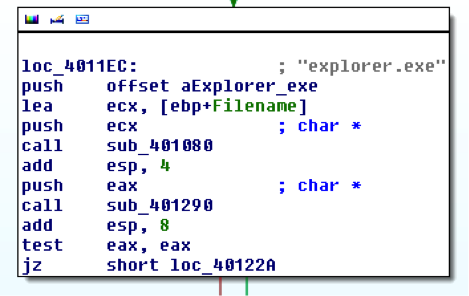
If the process is «explorer.exe» the «sub_401000» function is called:
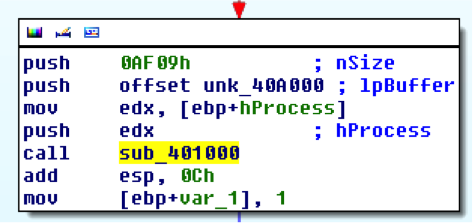
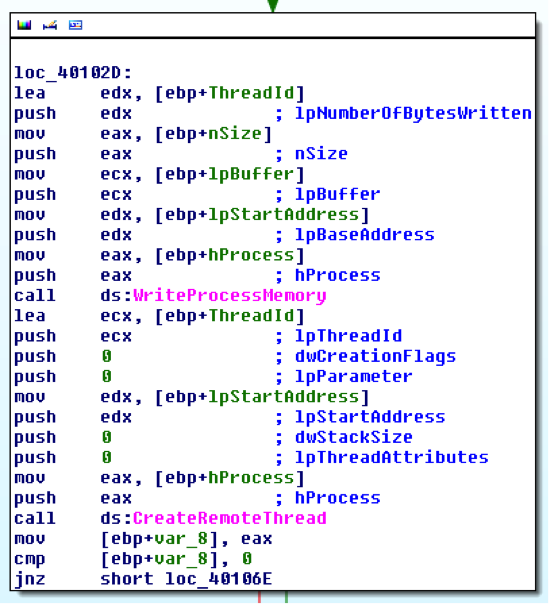
This function injects a piece of code using the «WriteProcessMemory» in the “explorer.exe” process and then executes it by calling «CreateRemoteThread».
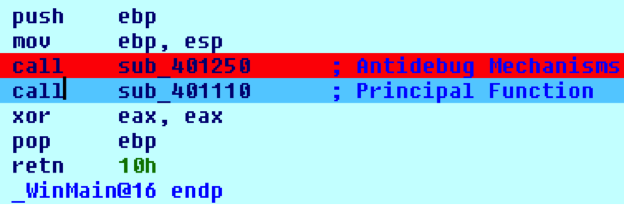
The next thing to do was to see what portion of code was injected by this function and what actions were performed. For that I started to debug the program. First I put a breakpoint in the function that containing the anti-debug techniques:
Then I changed the EIP to point to the following function:
Finally I put another breakpoint in the «WriteProcessMemory» API to see what code was injected:
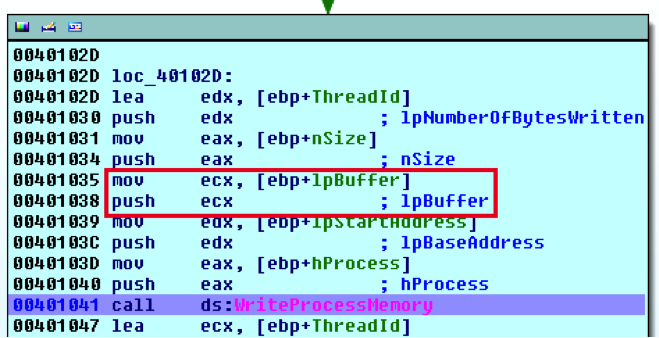
The injected code, is pointed to by lpBuffer. How this direction moves in ECX register, I went to the address to see which actions performed:
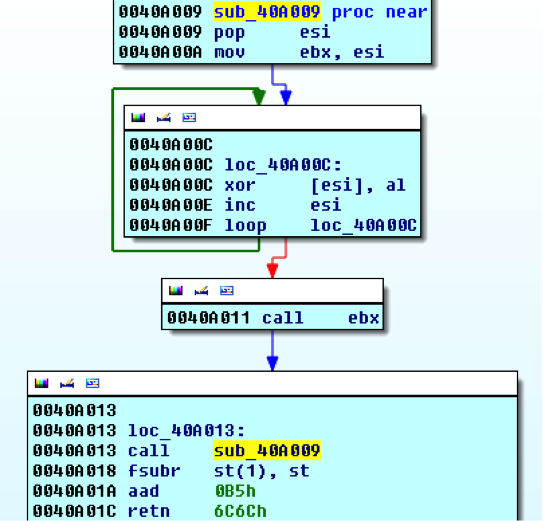
The beginning of the code that is injected into the “explorer.exe” process, as you can see, is a codedeciphering routine that appears later. From here there are several options:
- Put the CC instruction (int 3) at the start of the code to be copied into the process and set the IDA Pro in «set as just-in-time debugger» mode, so that when the injected code is executed and the program stops in the CC it is debugged by IDA Pro.
- Another easy solution is to put the EIP register pointing to the code to be injected and thus go debugging to see what actions it realizes once the code has been deciphered.
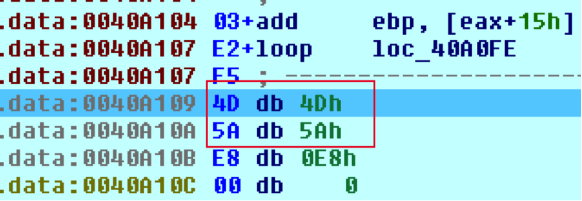
I did it using option 2. I started to debug the decryption routine while I saw the code that it was deciphering. At one point I saw the beginning of a PE file, because I saw it’s magic number 0x4D 0x5A (MZ):
At this moment I began to be clear about what it was doing, first find the “explorer.exe” process and then inject a code that was composed for a routine of coding plus a PE file, and then look if it was an executable or a .dll library
Knowing that it injected this PE file, what I did was a dump with the OllyDBG of the original file, once realized the whole routine of the deciphered, so I have the original, plus the decrypted PE file.
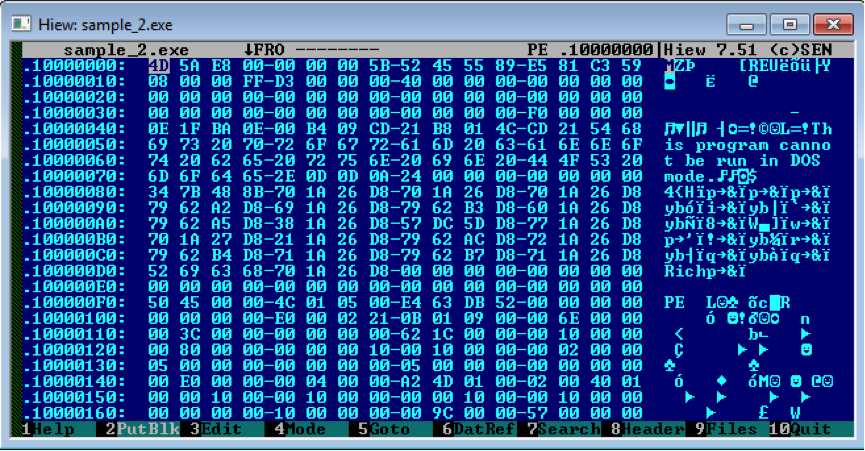
The next step would be to extract a PE file from the executable. This I did with Hiew:
When I had the PE file injected into an executable, the next thing I did was to make a static analysis with IDA Pro
The first thing that you see when you open the file with IDA Pro is that it was a .dll library as we showed the DllMain() function.
Another interesting function contained in this library was «URLDownloadToFileA», which meant that a file is download from Internet.
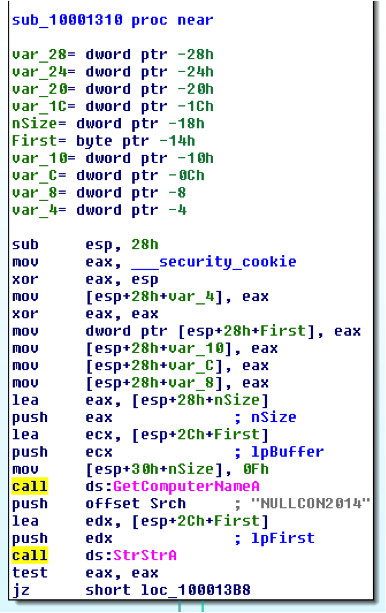
Analyzing the file statically you could see that firstly it was obtaining the name of the local host using the «GetComputerNameA» and comparing it to the string «NULLCON2014». If it matched with this string, continued executing actions, else, it ended:
If the name was correct «NULLCON2014», the following thing that it was doing was getting the current system date by calling «GetSystemTime». Then it made comparisons to see if the date was 03/03/2033:
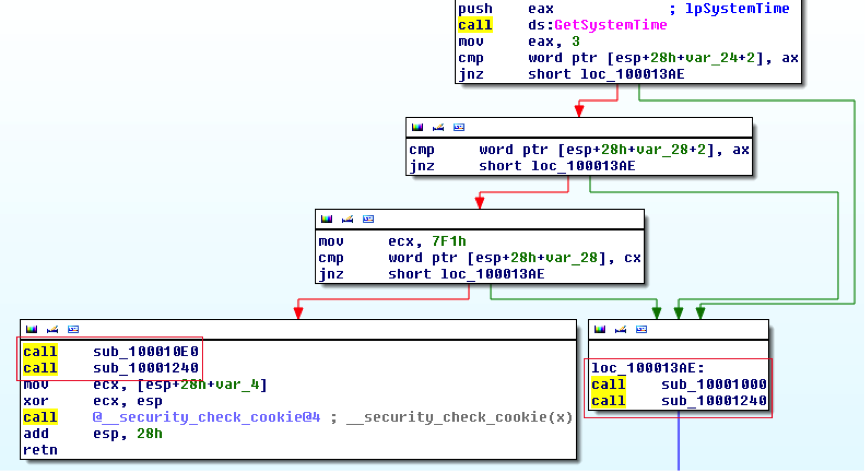
Depending on whether the date was correct (03-03-2033) or not, it make the request to a specific URL or another.
If the date was incorrect the request was make to:
- http://ctf.nullcon.net/NaN.php
However, if the date was correct it make the request to the url that you returned the flag to get this challenge successfully:
- http://ctf.nullcon.net/data/2014/rev/APT31337.php
For these requests to be successful they had to be performed by a correct «User-Agent»:
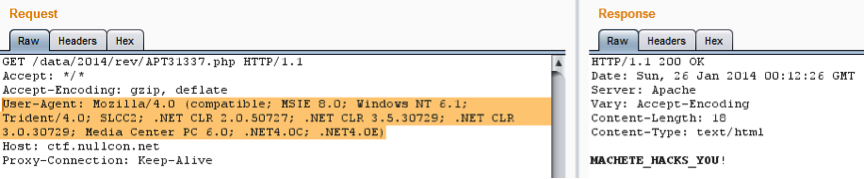
Finally, we can see that the Flag is MACHETE_HACKS_YOU!